Navigating Networked Ecosystems
Black Boxes are closed systems and proprietary technologies whose workings are kept secret from its users. The government employs black boxed technology in the surveillance of its citizens, and the The Internet itself, born out of America’s military-industrial apparatus, stands as monument to its own shrouded processes. Created by a notable mix of east coast and west coast minds, its central innovations center around “packet switching.” Packets divide data into containerized bits that make transmission quicker, scalable. The Internet gives an illusion of openness and freedom, but the protocols that dictate the movement of packets limit the security. What do these flaws leave vulnerable?
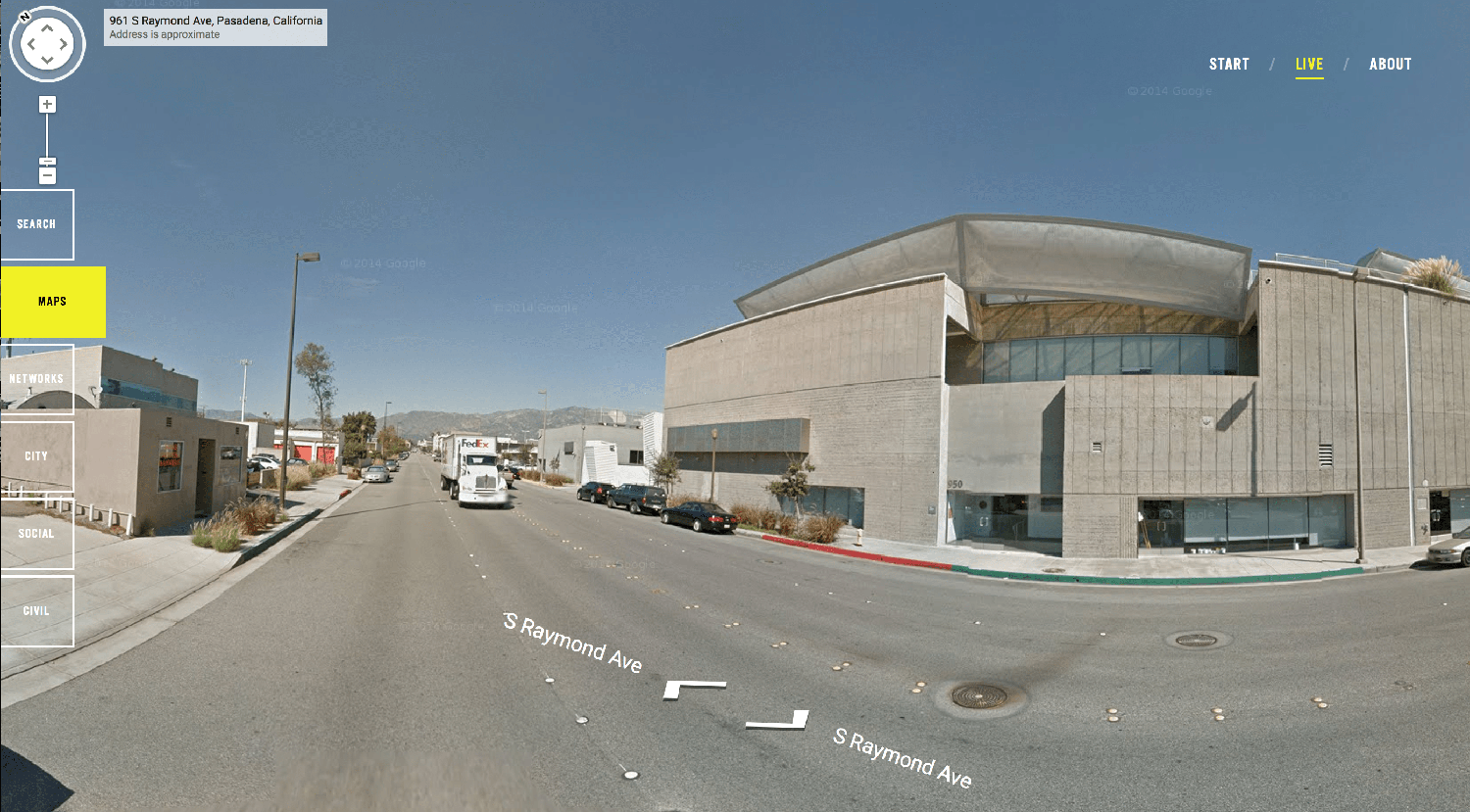
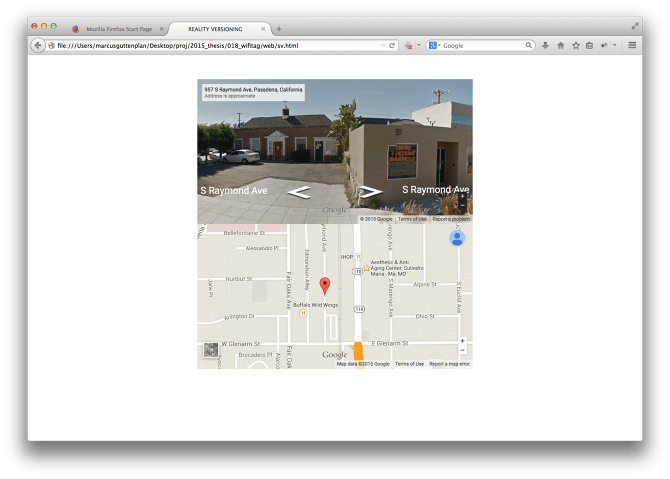
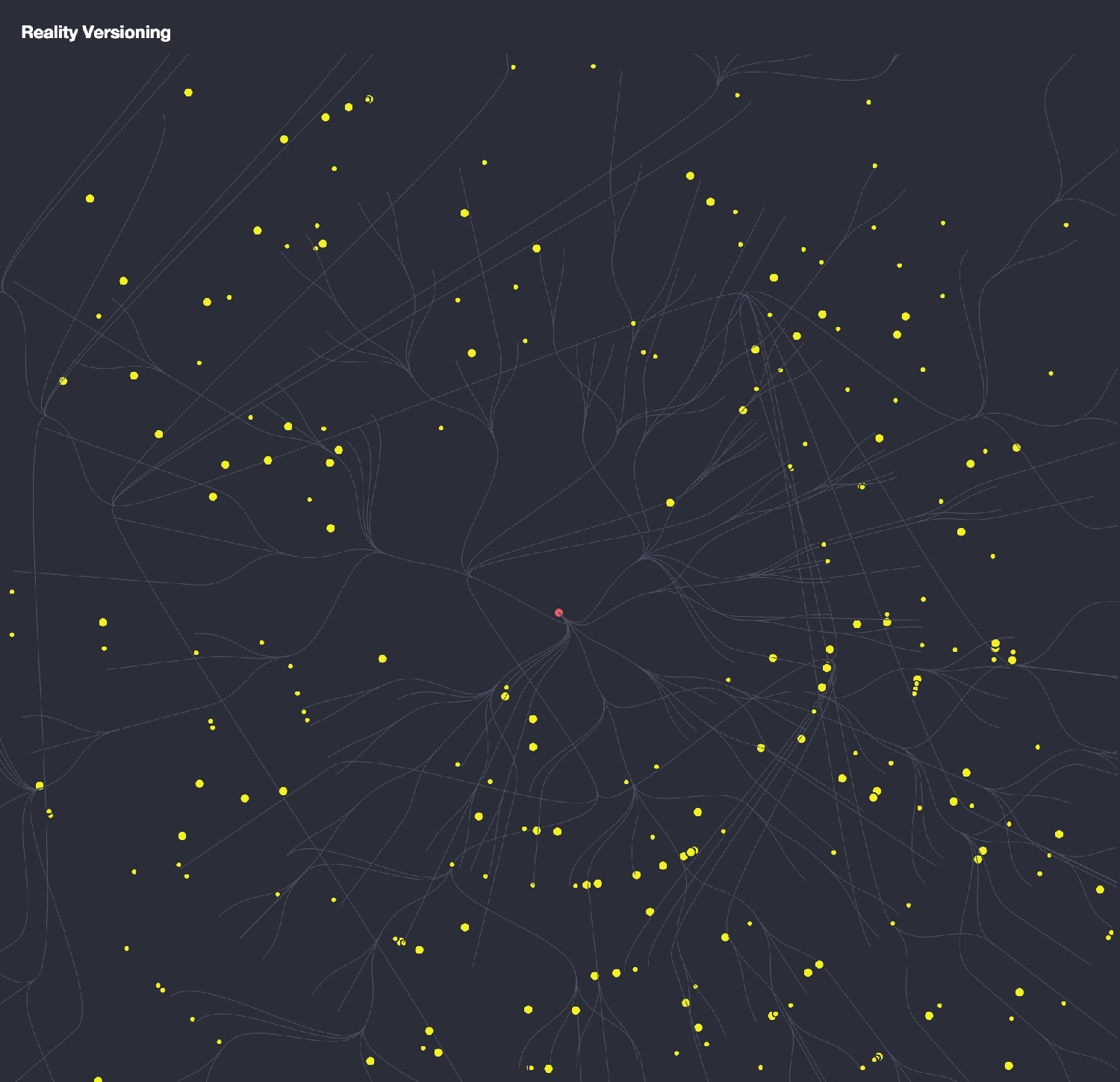
Personal geographies, for one. Our devices are constantly searching for something familiar -- a recognized wifi network -- and broadcast signals constantly. The interconnection of everything has created a parallel reality that contains all of our information but does not contain “us.” By making information dimensional, WiFicLAN serves as an alternate cartography for navigating the borderlands between physical and digital space. Even with adequate protection, modern networks are prone to subversion. By demystifying the black box, users are granted access to use and misuse high-technology in productive ways, creating unique solutions to novel problems with existing devices.

Community Sousveillance
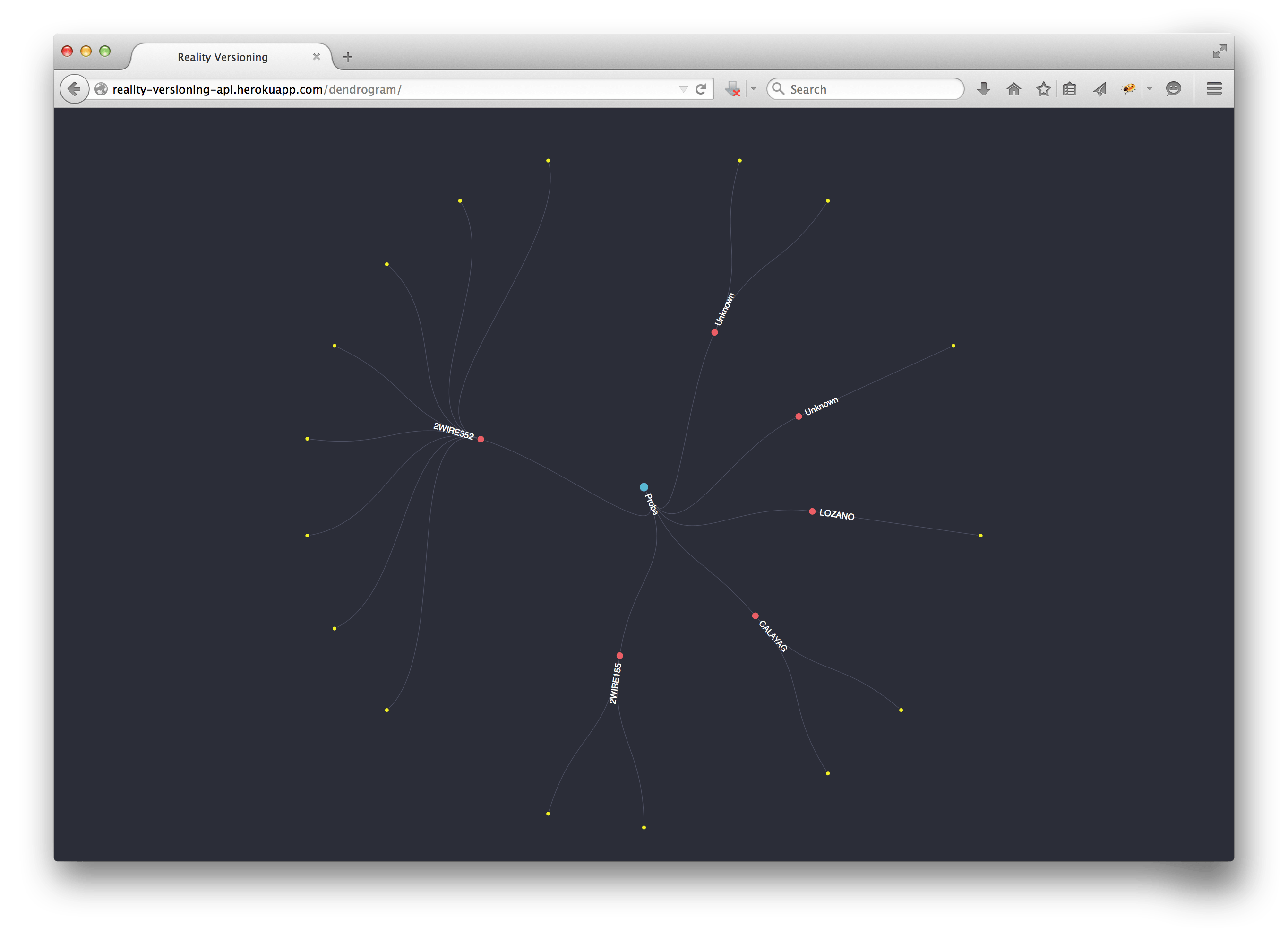
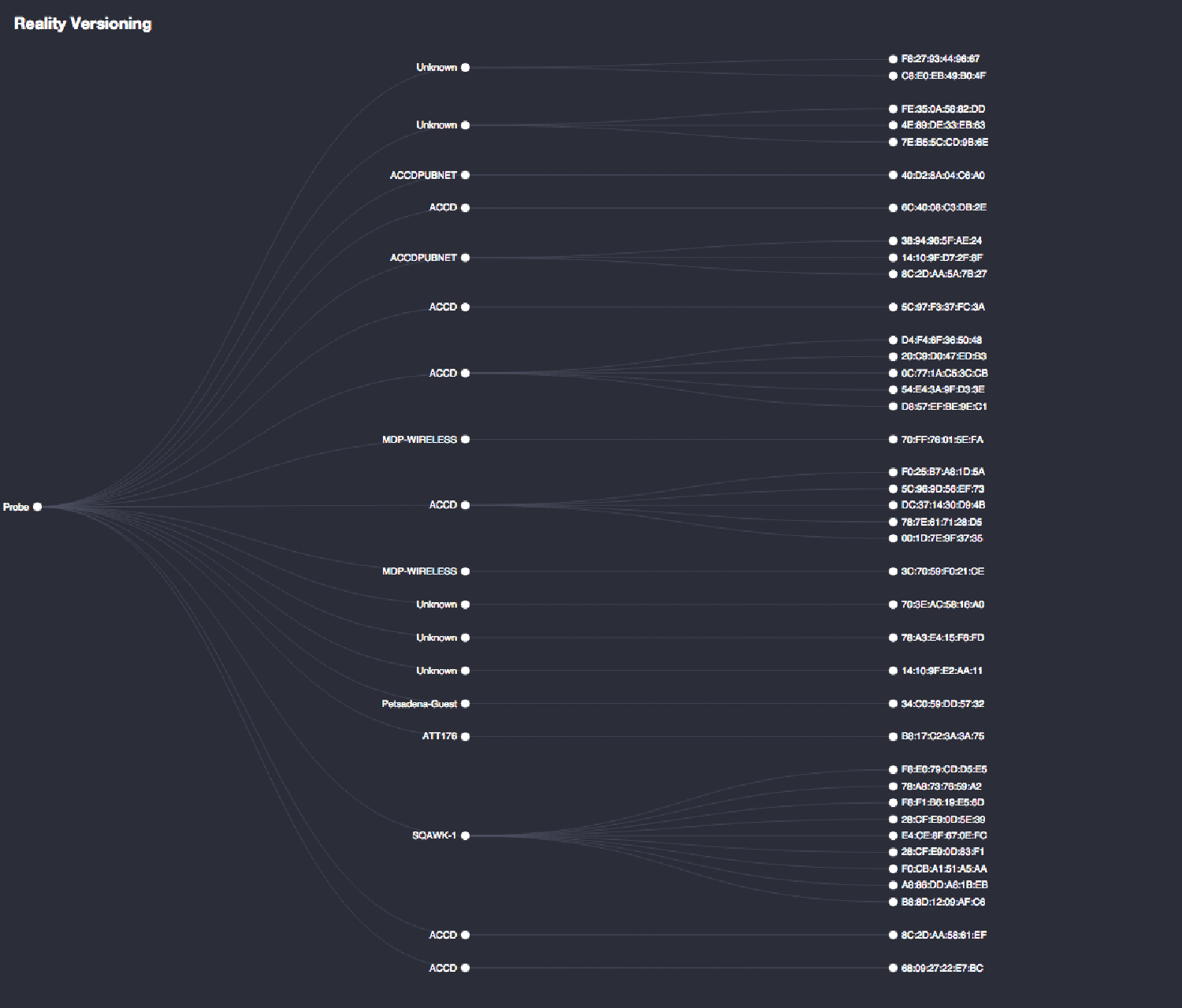
Along with broadcasted beacons giving away users' wifi histories, location data and the hardware addresses of associated devices are accessible via broadcast signals. Taken together, the information creates a coarse image. Wardrivers and warwalkers have been using these techniques for decades, ending up with detailed maps of wireless density. Google mapping vehicles also carry out wireless reconnaissance, adding more granular depth to their "deep map."
On a planetary scale, information generated by Internet and phone usage “IRL” accrues in the cloud and on the servers of government agencies. Binary bits with hyperlinks to coordinates and unique IDs, grains that map invisibly onto reality. Digital sediment settles, grows, and becomes dimensional. But we lack the means to adequately view and make use of this dimension. Enterprise-scale solutions can aggregate, and search for patterns, but these tools are expensive and inaccessible. Is it possible to use open source services to build user to user networks?
Unboxing Black Boxes
The continued hacking of national databases, from google to the Office of Personnel Management, only exemplifies this trend. Open Source Intelligence (or OSINT), is widely practiced in the intelligence community but fails to address and respond to "cyberthreats." In many ways, this data is useless. But to marketers aggregated data sets of millions of users' preferences and habits are a treasure trove of marketable insights.
In an interconnected world, the flows of illicit and legal web traffic all flow through the same infrastructure. Current web infrastructure -- the TCP/IP protocol -- is unsafe in nature, and its seams permit malicious and novel appropriation of the system by rogue agents. As it stands, the entire workings of the network are unclear to many daily users, and the lack of comprehension leads directly the plundering of underprotected information.

Infrastructural Disobedience
The Internet serves as the infrastructure of the state, a communication and commerce tool that drives the economy; supporting the superstructure of the political and legal systems that constitute the government. In many ways, with government agencies inhabiting the digital sphere more completely, the imperial superstructure begins to exist inside of the infrastructure.
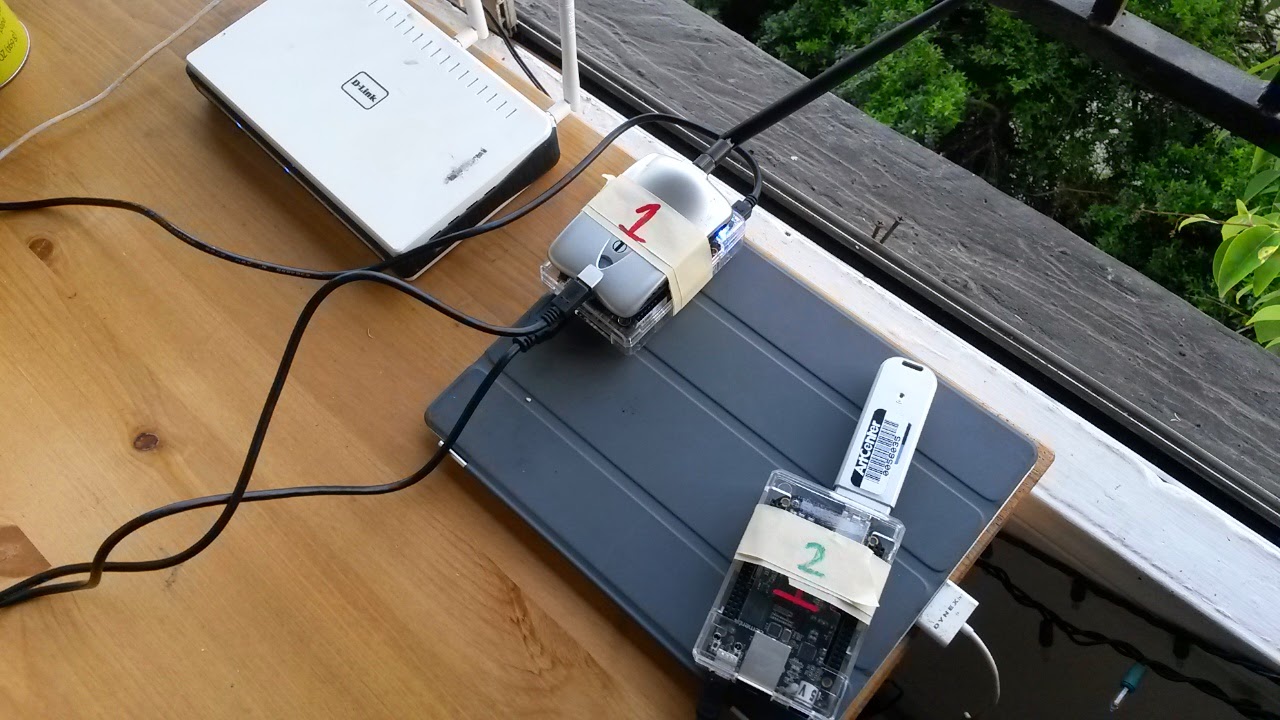
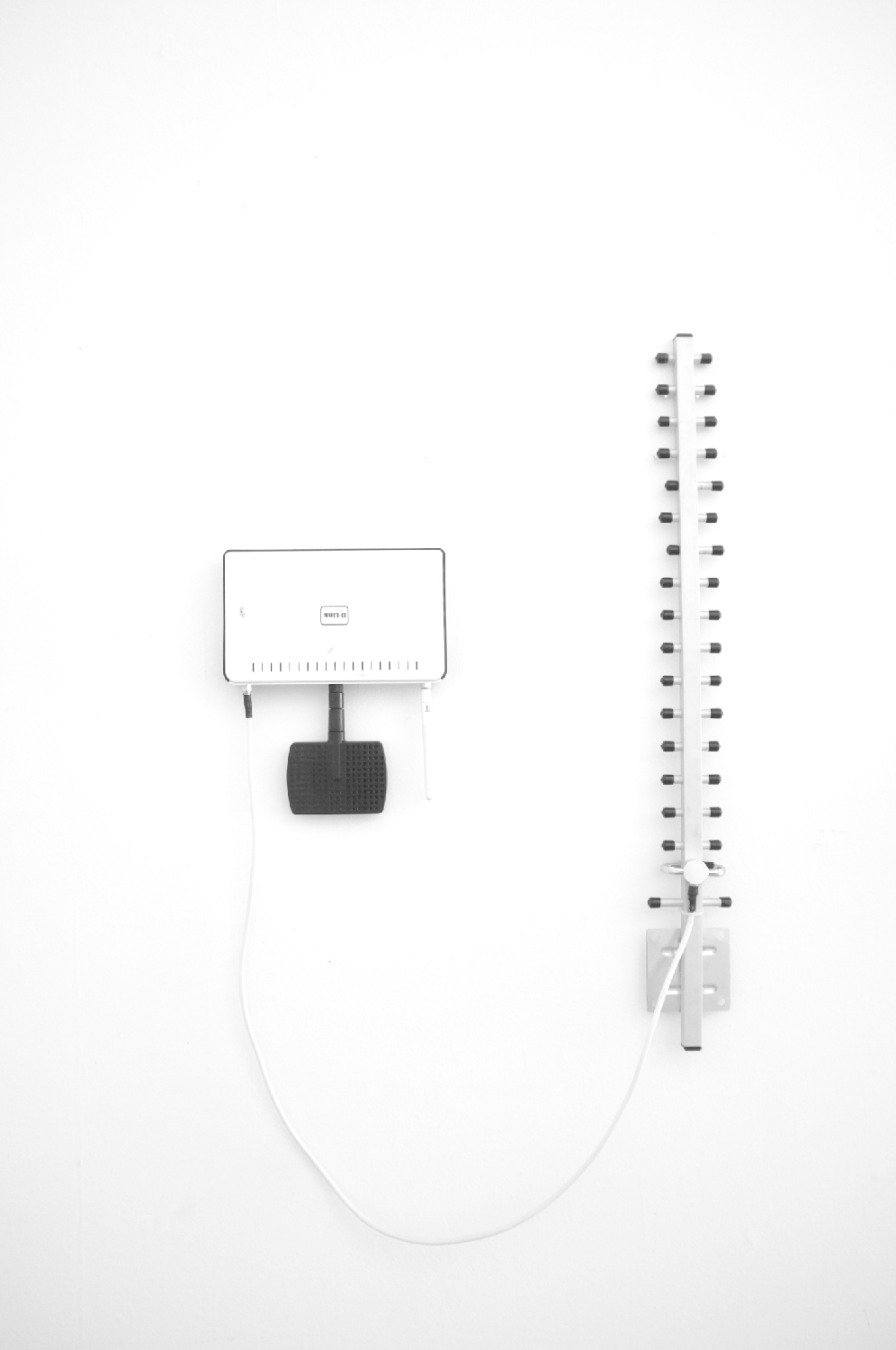
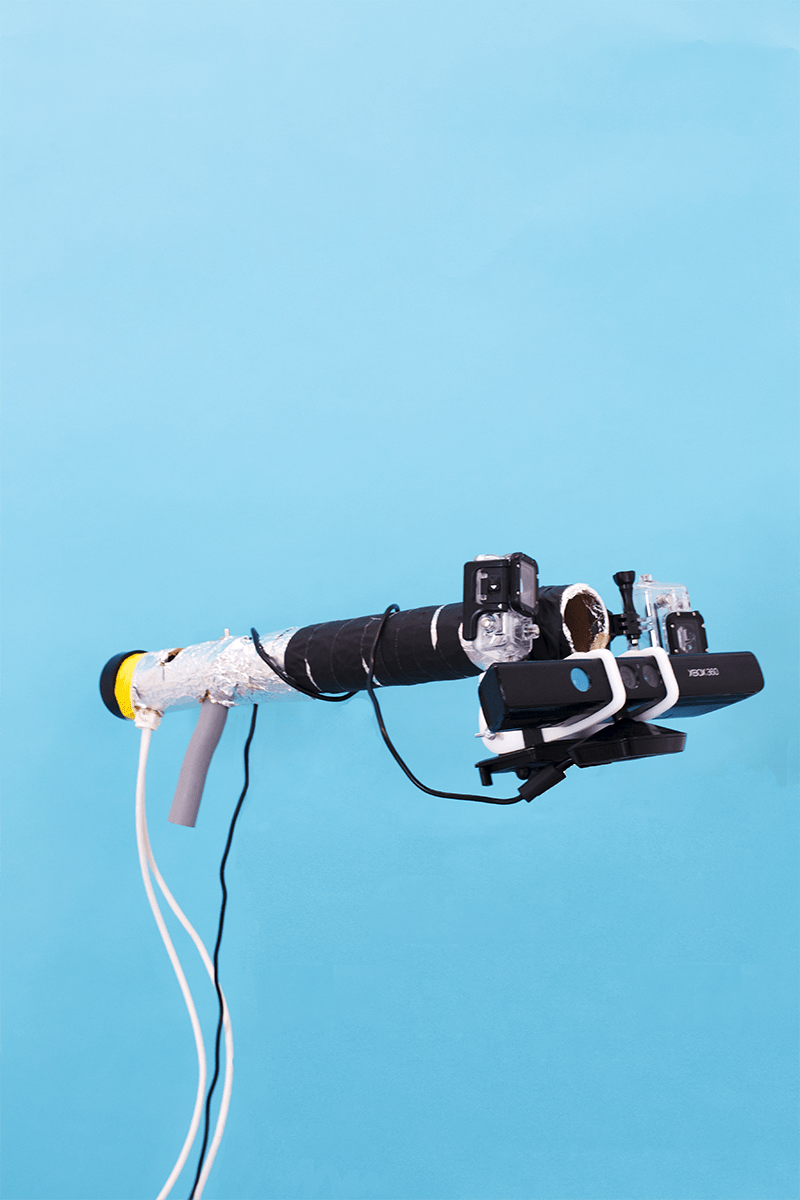
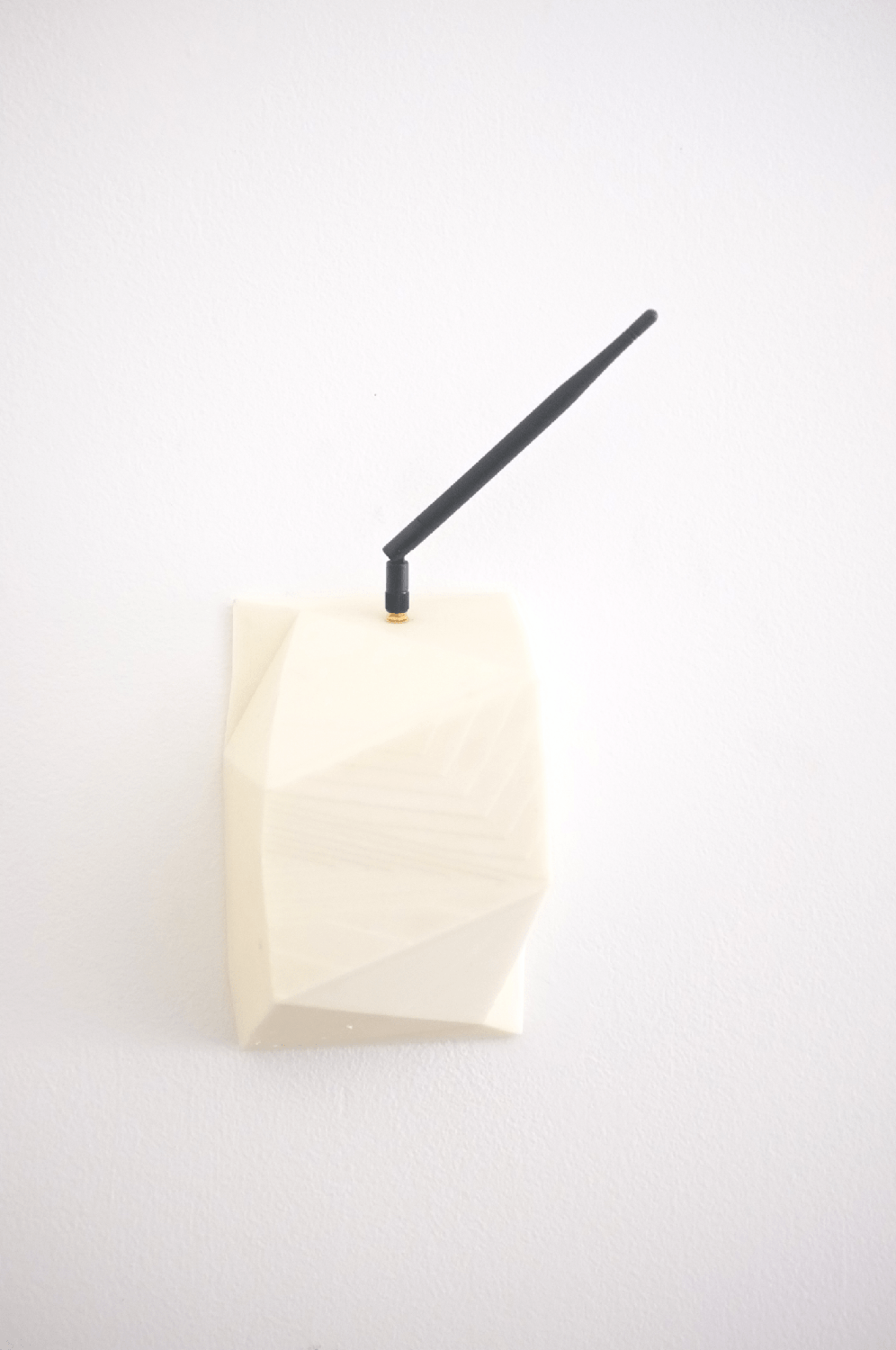
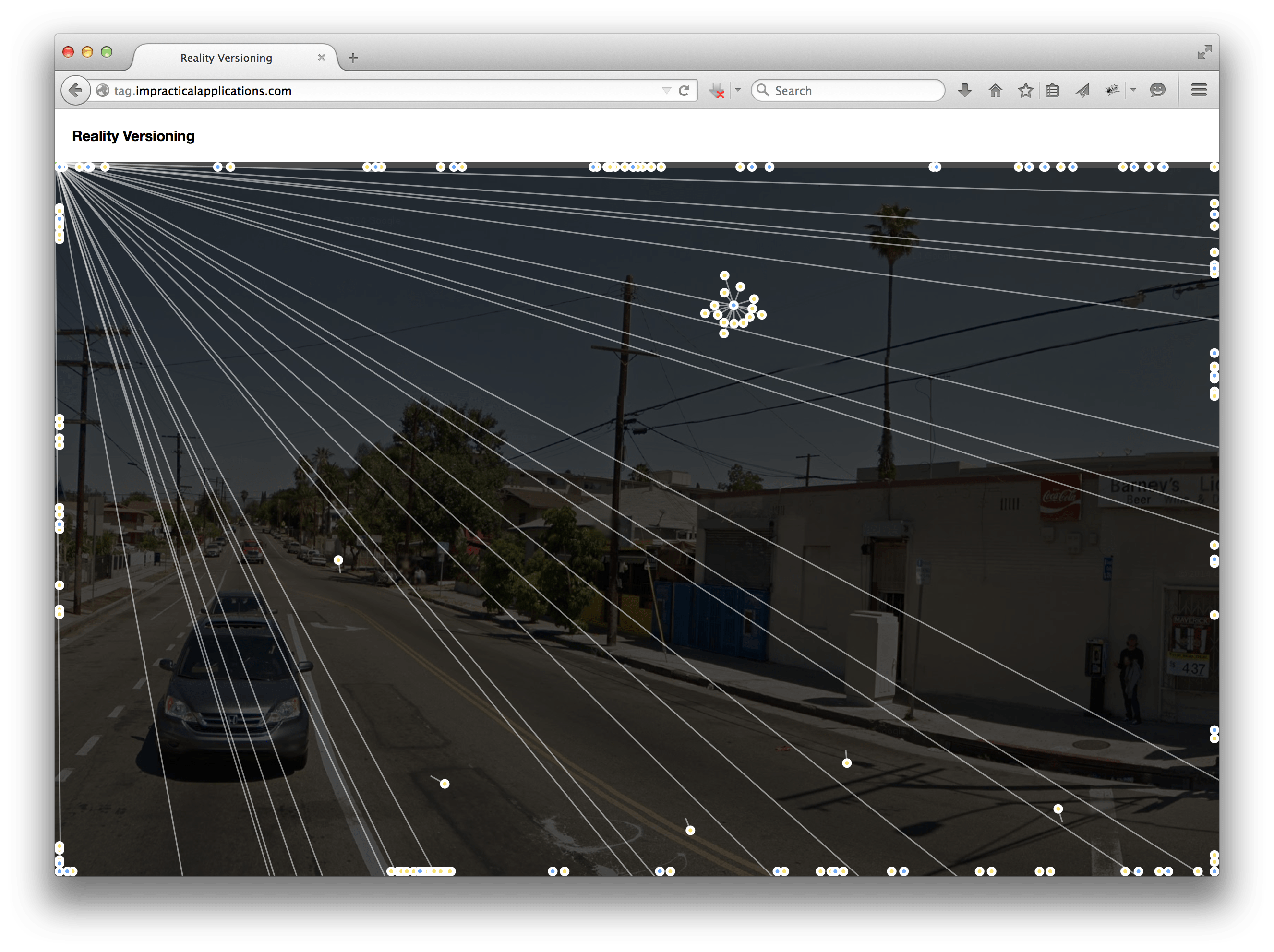
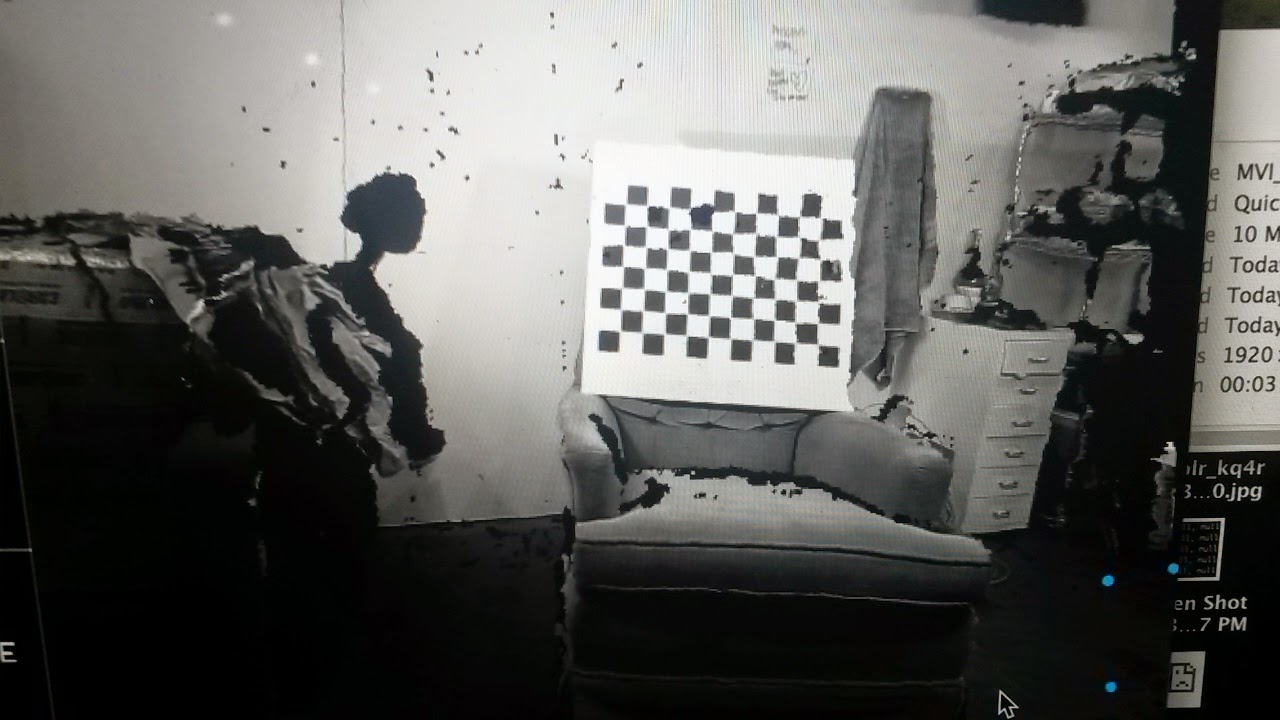
Using a couple of beaglebone black development boards as embedded computers, I set out to subvert existing networks and to create my own subnetworks. Each board runs linux, making them cheap brains that can interface with just about anything. Configured as tiny penetration testing platforms, the boards had the ability to autonomously map networked space, as well as perform offensive attacks at the physical and network layers.
Reality Versioning
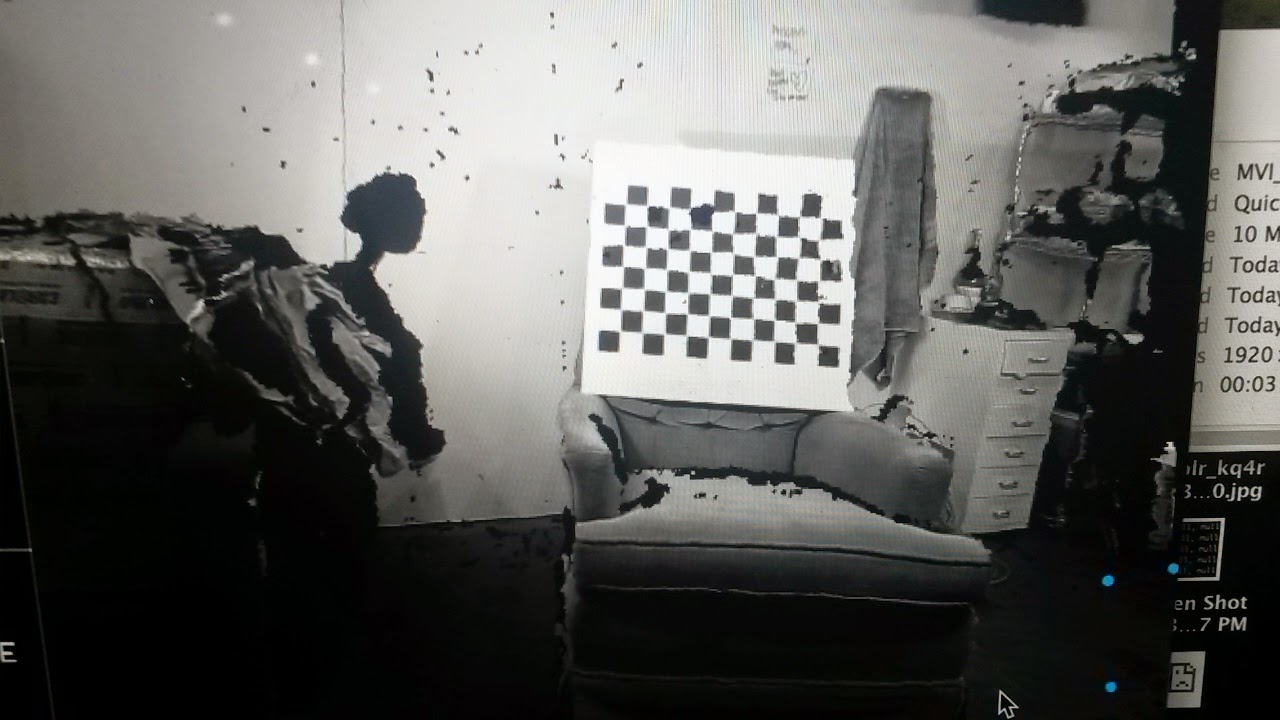
Even used passively as a sniffer and pinger, the board provides access to a world of information. Listening for any and all broadcasts, you start to get a sense of density. All of our devices are all talking to each other, and they're doing it often.
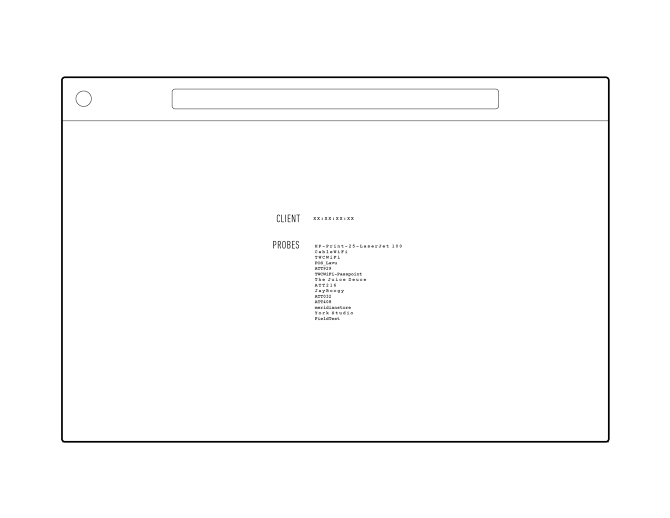
Inside of these innocuous-looking strings of numbers and wifi SSID's lies access to deeper and more personal information. Passwords passing in the clear can be discerned, and with a little more effort the beaglebone, acting as a man in the middle, can replace the content of web pages and deliver specific payloads. In a much less sinister situation, a domestic setting, a tiny computer like the beaglebone can be used to command and control your personal internet of things. Further, it could be used to distributed networks, and do so in a way that encrypts traffic using tunnels.
One of the biggest problems with this system is the need to remotely connect to and communicate with devices; and an even larger problem in the infosec community at large as the internet of things scales is user experience. The most powerful tools reside on the command line. To work around this, I collaborated with friend Derek Rushforth to build an API and a node.js based web app to monitor feeds from the boards and execute commands. Creating custom tools at every step, from the additional packages on the linux boards to the front and back end of a web app, proved that an average user could basically recreate the functions of a government black box commonly used for surveillance (the NIGHTSTAND and SPARROW II tools from the NSA ANT catalog).
Personal